Shepherd360
It is a cloud-based security infrastructure solution that addresses the safety needs of businesses and leverages them with physical security control. From safeguarding all critical assets to proactively addressing potential issues, this digital security system works as an all-inclusive solution.
Shepherd 360 not only focuses on securing essential systems but also delivers the most advanced security needs at the best value.
- Country United States of America
- Service
- Industry Multiple
Process Followed
The demand for functional physical security information management systems has upsurged in recent years which is undeviatingly making the app development companies the fastest-growing segment in the industry. Being one of the prominent app developers, QSS Technosoft considers improved enactment of cutting-edge solutions and thus strategises the app development process accordingly.
Problem Identification
Feasibility study
Solution Implementation
Challenges
Final Outcome

Problem Identification
The considerations which decide the functional areas of an organization always appear a bit complicated. Security infrastructure solutions should not only manage compliance needs but also be able to secure infrastructure with best-in-class functionality. In order to eliminate this and all such security problems, the QSS Technosoft team forged ahead with the client's idea of making a well-regulated security management system.
- Optimize physical security infrastructure
- Enriched with hardware and software agnostic system integrators
- Provides protection against high-volume threats
- Leverage business with the accurate security support module

Feasibility Study
While discussing major components of the app with the client, we realized that among all the modules, state-of-the-art artificial intelligence and digital sensors to monitor the real-time threats is the need of the business at the moment. With the amalgamation of new-age tech stack and pre-eminent programming language, the QSS Technosoft eyed to develop a secured native mobile application.
- Tailored to secure various infrastructure verticals
- Backed with highly versatile servers with network security
- Compliance to industry standards
- Proactively identify and patch susceptibility
- Intelligent data protection
Solution Implementation
User research
We surveyed various small business groups and tried to understand what they think of a tool that optimizes physical security infrastructure and safeguard the confidentiality of business information. This helped us understand the wide viewpoint of those who are part of daily organizational activities.
Product discovery workshop
Validating a product hypothesis is one of the most challenging lookouts for any business. Although, expanding the product line and getting the most out of the idea is not as difficult as many think. To properly reflect the product’s vision what majorly needs to be done is to align the well-thought-out strategy. With that said, the QSS Technosoft team, before getting into the development of the product, organizes the product discovery workshop in the presence of every project team member.
During the hands-on workshop, all the involved members discussed each minor detail related to the project. Whether it is about specific design problems or comprehensive evaluation of technical requirements, they addressed all the critical issues and effectively came up with an evolutionary roadmap based on the discussion. The discovery workshop went on for one week long and with the help of it, the team was able to create a vision of the product.

Competitor Analysis
It is believed that the better you understand your competitors, the more beneficial your product will be. Going by this theory, we inspected the market and tried to understand the strong and weak point of the already available similar solution.
Sample Interview Questions
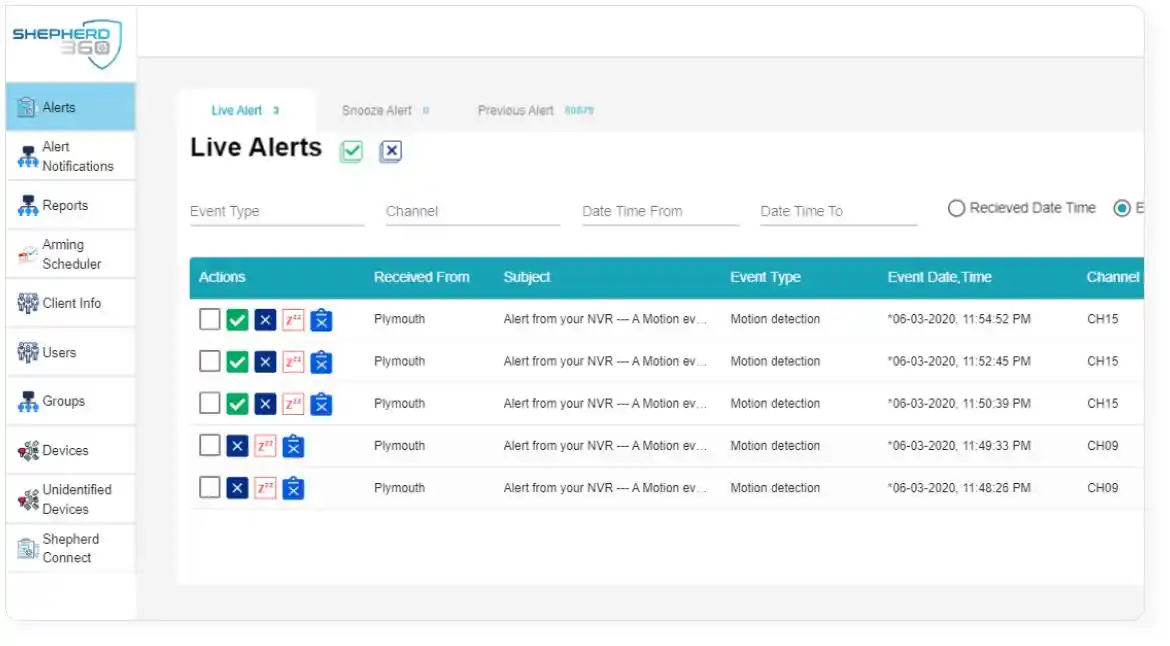
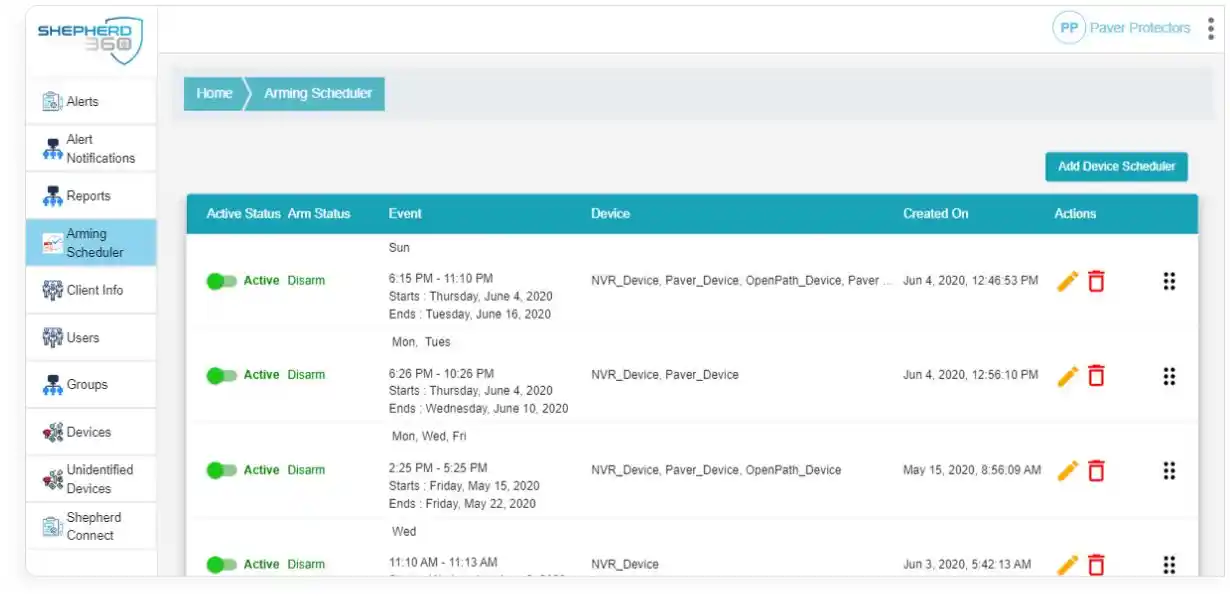
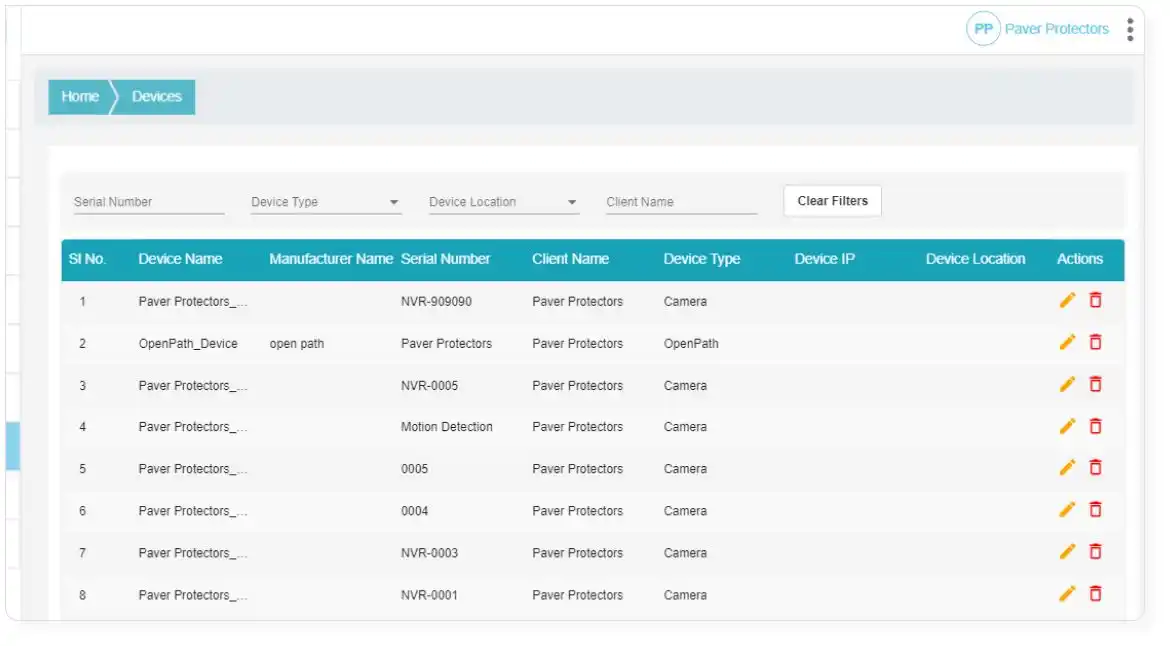
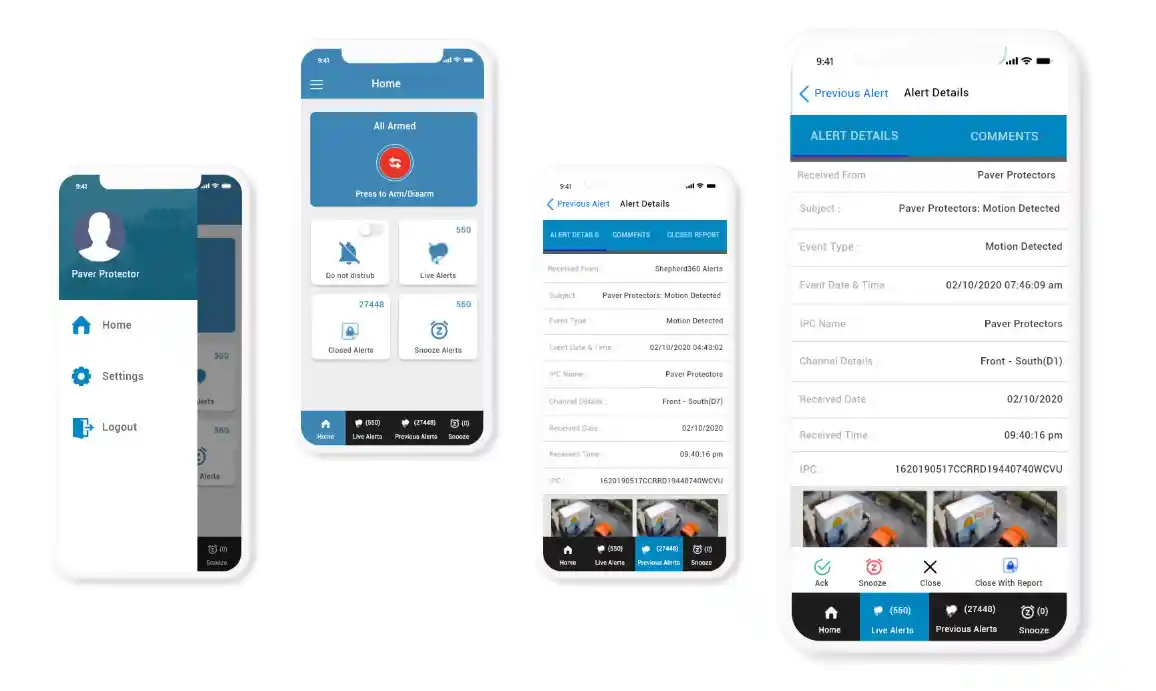
QSS team has developed a AWS cloud-based physical security information management system which manages all security operations from a single screen.
After capturing all the basic requirements and acquainting clients with wireframes, our in-house team of app developers executed the work and eventually developed a cloud-based physical security information management system which manages all security operations from a single screen. Some tech stacks we used are- ReactJS, C#.NET, PinPOint, HTML/CSS, MSSQL, AWS, Android, iOS, RabbitMQ.
Some fuctionalities added are-
-Tailored to secure various infrastructure verticals
-Backed with highly versatile servers with network security
-Compliance to industry standards
-Proactively identify and patch susceptibility
-Intelligent data protection
-Enriched with a highly advanced user-friendly interface
-Combines all the software modules in a single location
-Flexible setup for specific roles in security
-Extensive reporting capabilities
-Tailored to meet specific security requirements.
The client wanted a well-regulated security management system to fulfill objectives like-
-Optimize physical security infrastructure
-Enriched with hardware and software agnostic system integrators
-Provides protection against high-volume threats
-Leverage business with the accurate security support module.
Security infrastructure solutions should not only manage compliance needs but also be able to secure infrastructure with best-in-class functionality. In order to eliminate this and all such security problems, the QSS Technosoft team forged ahead with the client's idea of making a well-regulated security management system.

The Challenges
Every software solution has its own set of features and issues. It is nearly impossible to not come across any roadblocks while developing the solution as per market standards. Our team of well-versed developers, programmers and every member involved in the project too faced difficulties in configuring technical capabilities.
- Minimizing theft or misuse of data
- Adhering to the needs of an optimized and shielded operations
- Reducing the risk of regulatory non-compliance
- Allow organizations to efficiently manage all physical security
- Provide customized optimization of assets
Final Outcome
After capturing all the basic requirements and acquainting clients with wireframes, our in-house team of app developers executed the work and eventually developed a cloud-based physical security information management system which manages all security operations from a single screen.
- Enriched with a highly advanced user-friendly interface
- Help in building management and operations
- Combines all the software modules in a single location
- Flexible setup for specific roles in security
- Extensive reporting capabilities
- Tailored to meet specific security requirements

Information Architecture
Technology Stack
 MySQL
MySQL
 CSS
CSS
 HTML
HTML
 AWS
AWS
 Android
Android
 React Js
React Js
 PHP
PHP
 PinPoint
PinPoint
 Ios
Ios
 Rabbit Mq
Rabbit Mq
"I am overwhelmed with the enhanced service of QSS Technosoft. They have an amazing bunch of tech bugs who mould the app with new-age technology and made it blossom in the market."